Phishing
Basics: What You Need To Know!
Ignore & delete suspicious emails immediately.
Forward spam and phishing emails to us here: spam@eku.edu
How to Recover if you become a victim - EKU Students
Visit this page for the latest phishing alerts.
Legitimate EKU IT emails:
- All official IT Notices generate from IT.NOTICE@eku.edu. Check the email address before clicking or taking any action.
- All official IT Notices contain the Keene Johnson logo at the bottom of the email. Delete all suspicious emails immediately.
In the event you became a victim of a phishing scam:
- If you submitted your email password, change that immediately here: mymail.eku.edu | Click "Change My Password" | In the event the phisher already reset it, bring your picture ID by Combs 208 or call 859-622-3000 and we can reset it for you
- If you were a victim, here is more information.
- If you submitted your EKU Direct ID/PIN: You may e-mail a request to have your PIN reset through your EKU e-mail account to registration@eku.edu or come in person to either the Registrar's Office on the main campus (Whitlock 239) or the Resource Center/Information Desk at any of the extended campuses. If you come in person, you will need to bring a photo ID. Telephone requests to reset your PIN cannot be accepted. This may take up to two business days.
What is Phishing?
Phishing is a type of deception designed to steal your identity. In phishing scams, scam artists try to get you to disclose valuable personal data-like credit card numbers, passwords, account data, or other information-by convincing you to provide it under false pretenses. Phishing attempts can be carried out in person or over the phone, and are delivered online through spam email or pop-up windows.
Receiving the Email
- Know the online companies you deal with. When a suspicious email arrives in your inbox--THINK: it could be fraud, it's definitely spam, and it's not for you. Delete it!
- Look carefully at the subject line. Example: EKU will never send you an email headed "Account update act now." These messages may sneak through your spam filters because they appear to come from a reputable source, but that doesn't mean it's really from EKU or your bank or credit card company.
Looking at the Email
- Understand how the companies you deal with want to interact with you. For example, banks usually want you to access your account through their website--not an email link. "Phishing" emails stand out because they don't follow the rules.
- Practice safe browsing. Open a new browser window each time you log on to a website that displays personal information. When you are done, log out and close the browser window.
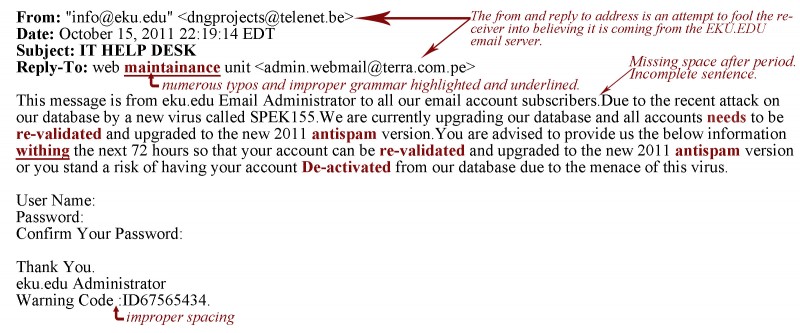
- Be sure to thoroughly read emails that say they are from companies you know. Watch for spelling and grammatical errors. Sometimes a real email will have an occasional spelling or grammatical error, but anything more than one is suspicious.
- Hover over email addresses and links with your mouse cursor and verify them. In some email systems, you can scroll over the different links in an email and see the actual contents of the link. If the email says PayPal, but the link says "www. paipall .com," be careful. And note: URLs can be disguised--so don't take a suspect link at face value. You can also Google and compare.
- Never enter your personal or credit information into a form in an email. If you feel the email is legitimate, visit their website and log in or call the company directly to provide the requested information. Don't click on the link or use any contact information in the suspicious email!
- Most "phishing" emails are not personalized. Expect good customer service from your online providers. Unless your name is "eBay User" or "Friends," if you receive a "Dear Customer" email, it may be time to move on. NOTE: EKU IT does use the salutation "Dear EKU Community."
Stay on Guard
- Read your bank and credit card statements - every one, every month to ensure your charges and debits are correct. Stay vigilant and report any suspicious activity immediately.
- Use and maintain your email protection software such as an antivirus.
Reporting
If you receive a message that our detection system doesn't pick up on, forward a copy to us: spam@eku.edu
Test your Ability to Identify a Phishing Scheme
There have been several email attempts lately that try to get users to reply with their email account and password. EKU will NEVER ask you to provide any account information through an email.
Spelling and Grammatical Errors Identified
What to do if you have Responded to a Phishing Email
- Call the Help Desk at 622-3000 or complete the IT Service Help Ticket