Spear Phishing & Whaling Attacks
EKU has been the target lately of spear phishing and whaling attacks. The definitions and examples below explain each type. There are also steps to protect yourself at the end.
What is a spear phishing attack?
These are a form of phishing which targets a particular individual to gain sensitive personal or business information. It is a social engineering attack in which a perpetrator, disguised as a trusted individual, tricks a target into clicking a link in a spoofed email, text message, or instant message. These can also be used to ask the victim to do something for them, such as buy a gift card for them. These can target anyone in the organization but used to gather personal details on their targets. Whaling is one type of spear phishing attacks.
What is a whaling attack?
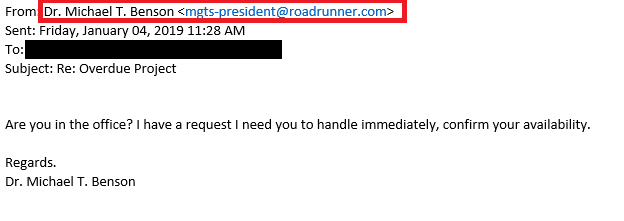
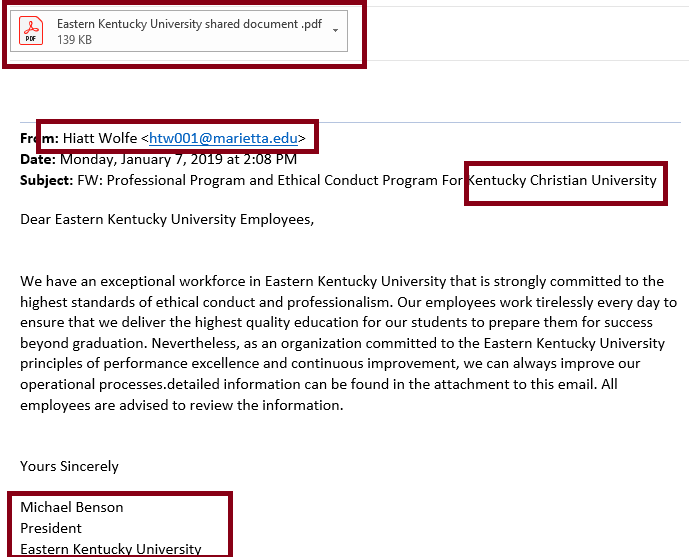
These are targeted attempts to steal sensitive information from a company such as financial information or personal details about employees, usually for malicious reasons. A whaling attack specifically targets senior management that holds power in a company or organization, such as a president, a CEO, CFO, CIO, or other executives who have complete access to sensitive data. It is called "whaling" because the size of the targets relative to those of typical phishing attacks, "whales" are carefully chosen because of their authority and access within the company. The goals of a whaling attack are to trick an executive into revealing personal or corporate data, often through email or website spoofing.
The difference between whaling and spear phishing is that whaling exclusively targets high-ranking individuals within an organization, while spear phishing usually goes after a category of individuals with a lower profile.
Types
Generally, these fall into these categories or a combination of:
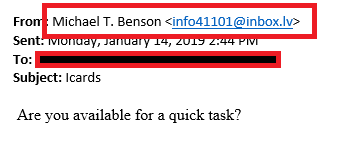
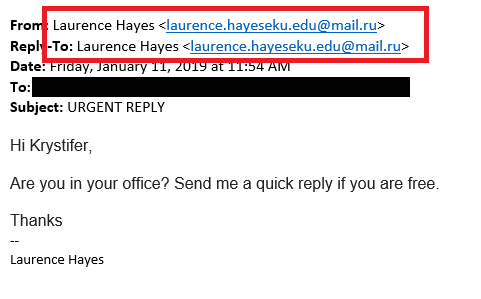
- Too busy to talk. The attacker spoofs the email address and asks for a quick favor in an email because they are too busy to talk. Generally, they are in a meeting and can't call. They may ask a question as simple as "Are you available?"
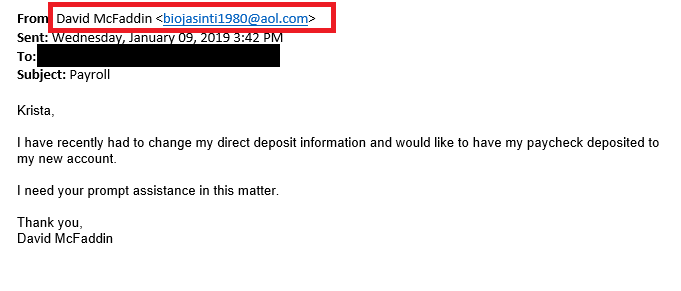
- Need the money fast. The attackers asked the victim to send a quick payment for them. These can include attached invoices to pay or ask for a wire transfer.
What is spoofing and masquerading?
Spoofing is a phishing method that involves altering the information in an email header to impersonate a trusted entity. For example, an email may have a known name of someone you trust, but be from an @gmail.com account. Links can also be spoofed to say one thing but if you hover over it, you will see the "real" URL or domain you are being directed to.
Masquerading involves creating email addresses that seem to belong to a company or person, but actually belong to a hacker. This allows that hacker to pose as someone else without that person ever being aware of their doppelganger. Masquerading accounts account for 72 percent of whaling attacks.
Examples
Protecting Yourself
- Always run an up-to-date antivirus/antimalware software to protect yourself.
- Always create long and strong passwords. Change them often and don't reuse.
- Never disclose your passwords.
- Don't open attachments unless you're expecting to receive them.
- Hover over links to see the full URL. If the destination differs from the text or the expected website, the link is spoofed and shouldn't be clicked.
- Preview the email address of senders when you receive a suspicious email.
- Always forward spam, phishing, and suspicious email to EKU IT: spam@eku.edu We look at EVERY message that we receive and in the unlikely event it is legitimate, we will reply and tell you.
- Remember, EKU IT will never request your login credentials.
- If you believe your EKU email account or EKU credentials have been compromised, immediately reset your password in EKU Direct (under the 'Personal Information' tab) and call the IT Service Desk: 859-622-3000
- These rules apply to email, text messages, and telephone calls. Always be suspicious of unsolicited contact.